We’re a people focused
organization
Who we are
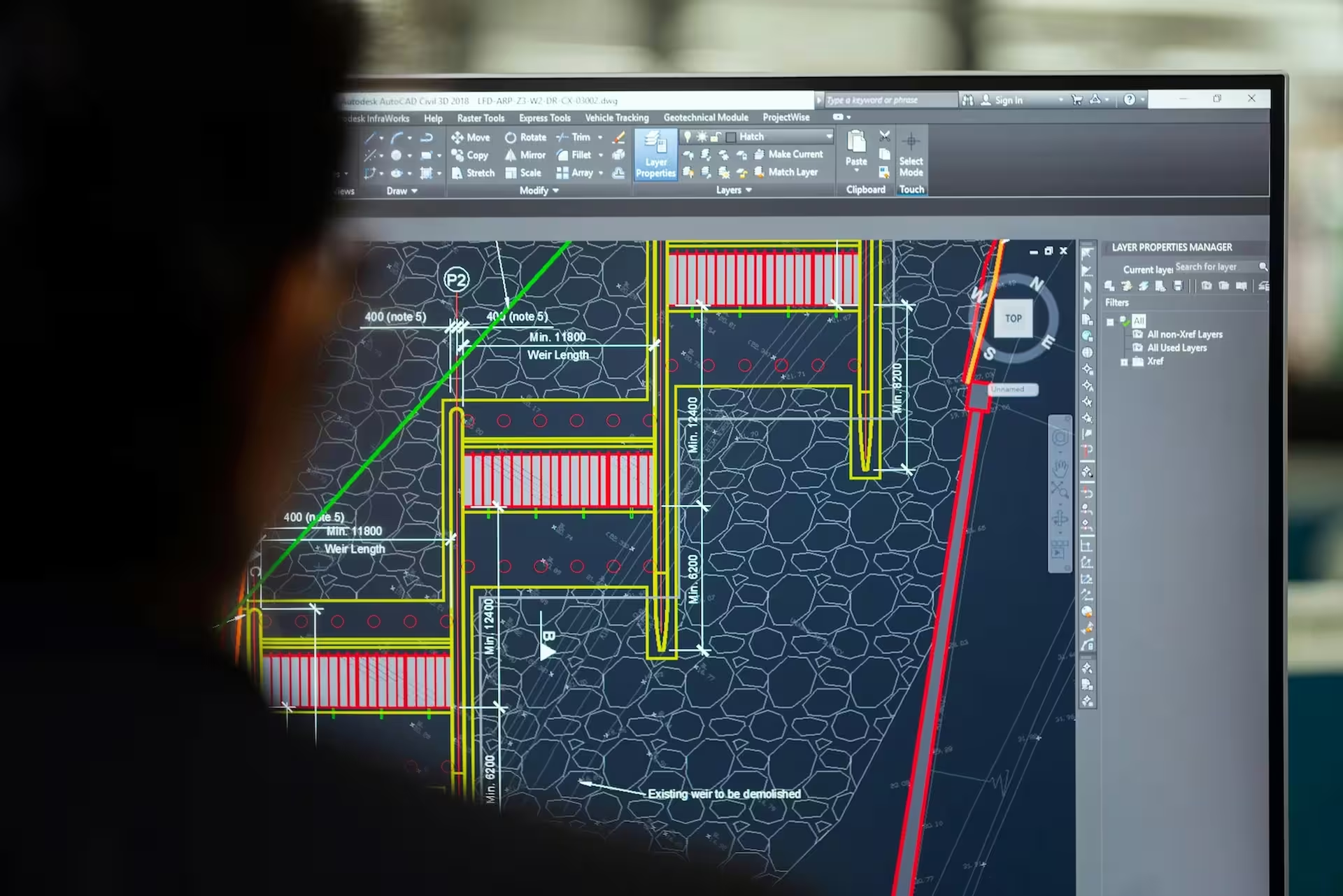
We pride ourselves on our flexibility and customer-centric approach. From day one, we place our customers in the driver's seat, ensuring that our solutions align precisely with their requirements and objectives. Unlike others, we prioritize integrity over sales pitches, never pushing unnecessary products or services.
Our company, provides you access to senior engineers ready to delve into the details and provide personalized support to every client. Whether it's troubleshooting a technical issue or strategizing for future growth, our team is dedicated to being in the trenches with our clients, every step of the way.
Established in December of 2010, Aspire Live has remained privately held for over 10 years, demonstrating our commitment to stability and long-term relationships. With a worldwide team, we operate on a global scale, providing innovative solutions to meet the diverse needs of our clients. As a trusted solution provider, we proudly serve Fortune 100 companies and small business alike, earning recognition as a top technology partner with leading technology providers.

Proudly owned and operated by a woman and a minority, fostering diversity and inclusivity in all aspects of our business.

Headquartered in LA and fully owned by American stakeholders, we are dedicated to supporting the local economy and workforce.

As a veteran-friendly organization, we prioritize hiring and supporting military veterans, recognizing their valuable skills and contributions.

Despite our growth and success, we maintain the agility and personalized service of a small business, ensuring tailored solutions and attentive customer care.